Target: Low-Impact. Why the New Federal Floor is Only the Beginning of Grid Resilience
Regulation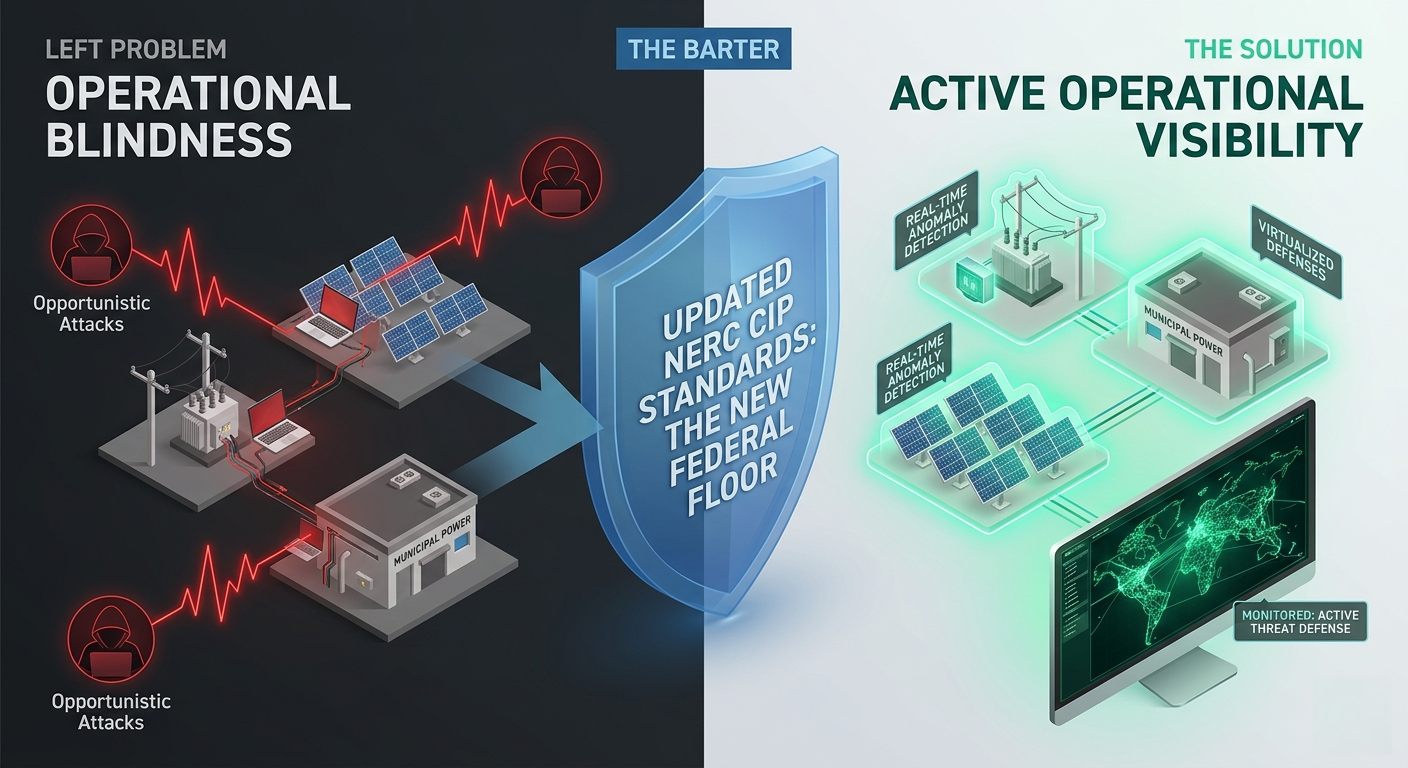
The "sophisticated nation-state attacker"is no longer the only variable in grid security. Recent data suggests a shifttoward a more chaotic reality: our critical infrastructure is being poked andprodded by opportunistic actors looking for the path of least resistance.
In the wake of two major industry reports and alandmark federal ruling this month, the message for grid operators is clear:treating "low-impact" assets as secondary priorities has created aliability that the government is no longer willing to ignore.
The Rise of the Opportunistic Attacker
Intelligence from Team82 (Claroty) intheir recent Analyzing CPS Attack Trends report highlights a pivotin adversary behavior. Attackers are increasingly bypassing the hardenedperimeters of major transmission hubs to target "low-impact" assets - municipal utilities, small substations, and DERs. These are not always complex"zero-day" hacks; they are often simple exploitations ofinternet-facing systems and default credentials.
This trend is validated by the Q1 2026 Nozomi Networks analysis, which identifies"operational blindness" as the critical failure point. When anattacker gains access to a Human-Machine Interface or a SCADA system, theimpact is physical. The report notes that geopolitical spillover is no longertheoretical, with disruptive operations now hitting smaller industrialorganizations and utilities that lack the visibility to see the threat coming.
The Regulatory Counter-Move: FERC and NERC Action
On March 19, 2026, the Federal Energy RegulatoryCommission (FERC) took decisive action to close these gaps byapproving a series of standards developed by the North American ElectricReliability Corporation (NERC). The distinction is functional: NERC defines the technical requirements, and FERC provides the legal enforcement.
Their joint focus is now squarely on the assetspreviously considered "under the radar":
- Eliminating the Low-Impact Pass: FERC approved updates to NERC CIP standards (specifically CIP-003) that mandate baseline security for low-impact systems. This includes required intrusion detection and robust password protocols - directly addressing the vulnerabilities identified by Team82.
- The Virtualization Mandate (Order No. 919): By approving 11 updated standards, FERC is clearing the path for utilities to move toward virtualized, cloud-based environments. This is a critical move for resilience, allowing for centralized security monitoring that legacy, isolated hardware cannot support.
- Redefining Control Centers: An updated definition of "control center" ensures that distributed assets are now legally required to meet higher security tiers, effectively expanding the protected perimeter of the grid.
Bridging the Visibility Gap
For the professional, these changes represent amassive shift from "compliance as a chore" to "security as arequirement." For the public, it means the grid is finally getting thedigital oversight it needs. However, a higher regulatory floor does notautomatically result in a secure grid.
The reports from Nozomi and Team82 make it clearthat the primary hurdle remains the visibility gap.Adversaries rely on the fact that many operators are "blind" to whatis happening on their OT networks in real-time.
Meeting the new NERC requirements is the baseline.Real resilience requires moving beyond static asset inventories toward activeoperational monitoring. Implementing Machine Learning foranomaly detection and passive, vendor agnostic monitoring is the only way to meet the new federal standards whileactually eliminating the blind spots that opportunistic actors rely on.
The "Great Grid Upgrade" of 2026 is atransition in philosophy: recognizing that any asset connected to the grid is apotential entry point. Solving for operational blindness is the only pathforward.